Array
(
[1536x1536] => Array
(
[width] => 1536
[height] => 1536
[crop] =>
)
[2048x2048] => Array
(
[width] => 2048
[height] => 2048
[crop] =>
)
[rta_thumb_no_cropped_420x] => Array
(
[width] => 420
[height] => 0
[crop] =>
)
[et-pb-gallery-module-image-portrait] => Array
(
[width] => 400
[height] => 300
[crop] => 1
)
[et-pb-post-main-image-fullwidth-large] => Array
(
[width] => 0
[height] => 0
[crop] => 1
)
[et-pb-image--responsive--desktop] => Array
(
[width] => 1280
[height] => 720
[crop] => 1
)
[et-pb-image--responsive--tablet] => Array
(
[width] => 980
[height] => 551
[crop] => 1
)
[et-pb-image--responsive--phone] => Array
(
[width] => 480
[height] => 270
[crop] => 1
)
)

Potentially every Intel processor sold in the last 10 years could have a critical security vulnerability that puts users at severe risk. It’s often these days that poor IT security comes down to something like human error, and lack of awareness on the users’ part....
Discover More
Two critical vulnerabilities were found in Intel chips that could result in a malicious attacker stealing your data, such as photos, emails, documents, browsers, and password managers. How can this affect you? The vulnerabilities called “Meltdown” and “Spectre,” can...
Discover More
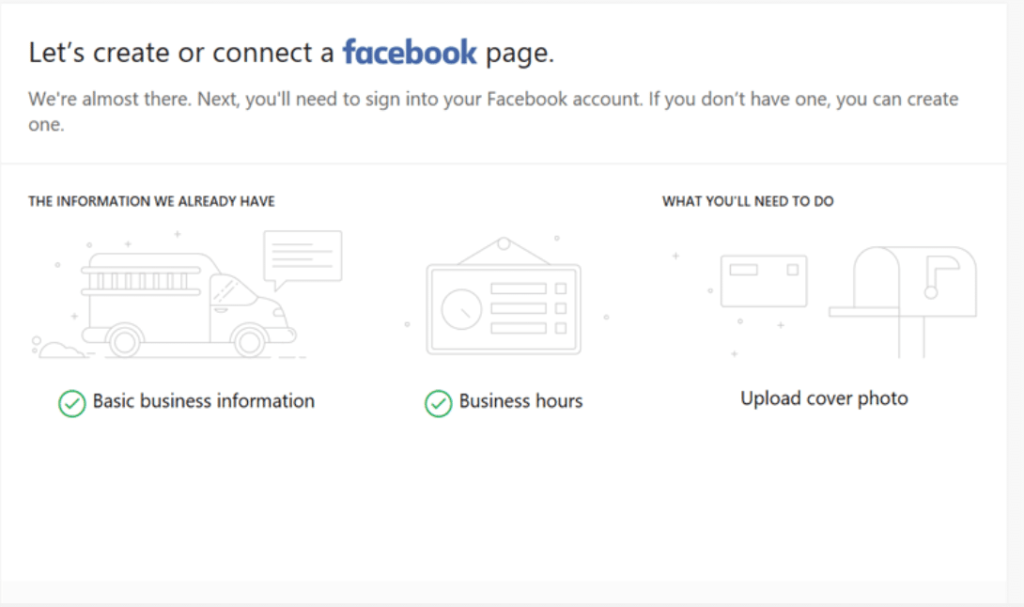
Get the Support You Need from The New Tools in Microsoft Office 365. To provide the growth small-and medium-sized businesses need, Microsoft has introduced a series of new applications and enhancements to their Office 365 Business Premium Subscription. These new tools...
Discover More

Scam phone calls aren’t a new thing, but today’s scammers are now bolder and more sophisticated. In 2010, more than 84,000 people reported phone-related scams to the Federal Trade Commission (FTC). Scammers can spoof phone numbers from your local area code or a number...
Discover More

Theft and fraud are serious causes for concern both in and out of the office, which makes education and awareness on the subject crucial. Cybercrime comes in many forms and uses many different tactics to put valuable data in the hands of hackers and scammers. Often a...
Discover More